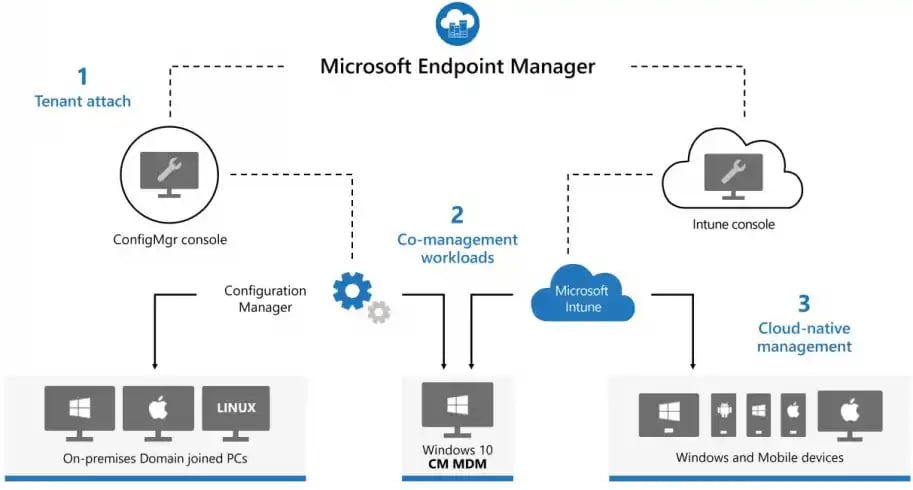
Co-Management
Attach your existing Configuration Manager deployment to the Microsoft 365 cloud, allowing you to manage Windows devices with both Configuration Manager and Microsoft Intune seamlessly.
Modernize your identity and device management with the Microsoft 365 E3 or E5 technology suite.
Our expert CloudServus consultants are here to help you make the most of EMS and E5 technologies. Whether through Intune, System Center Configuration Manager (SCCM), co-management, Azure AD, or Windows Autopilot, we ensure a seamless, secure implementation tailored to your needs.
Empower your organization with a streamlined approach to endpoint management through our expertise in Microsoft solutions:
Attach your existing Configuration Manager deployment to the Microsoft 365 cloud, allowing you to manage Windows devices with both Configuration Manager and Microsoft Intune seamlessly.
Maintain your on-premises Active Directory setup while benefiting from Azure Active Directory integration, providing a unified endpoint management system.
Simplify device and app management across all your devices—mobile, desktop, and virtual—with this cloud-based solution that controls user access and enhances security.
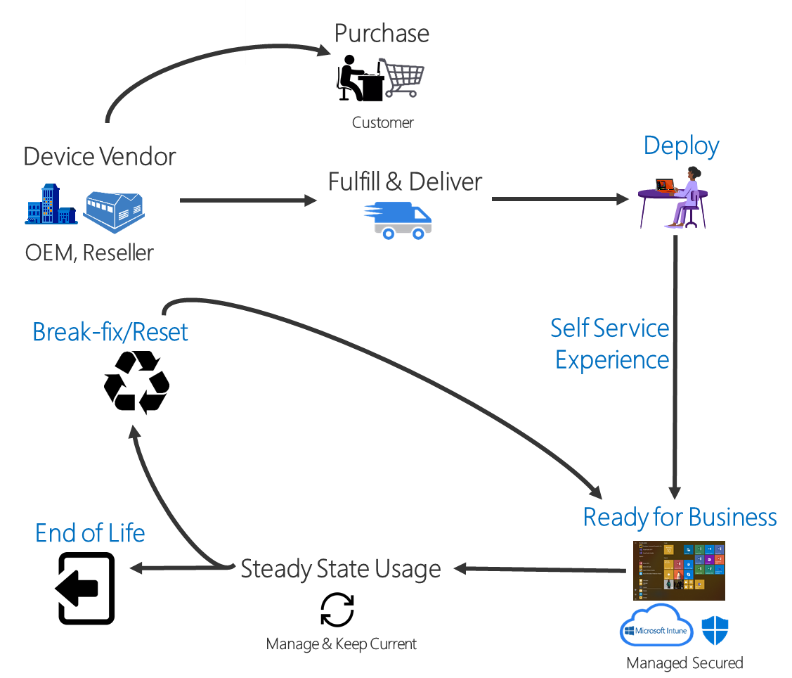
Set up, pre-configure, and manage new devices effortlessly. Autopilot prepares them for productive use and helps with resetting, repurposing, and recovery as needed.
Whether you’re transitioning from on-premises or taking the next step with Intune and Autopilot, our expert team is ready to support you.
Let's Connect
CloudServus’ expert team can help you determine the most appropriate endpoint management system for your organization’s needs.
Choosing the right endpoint management system is essential for a seamless device management strategy.
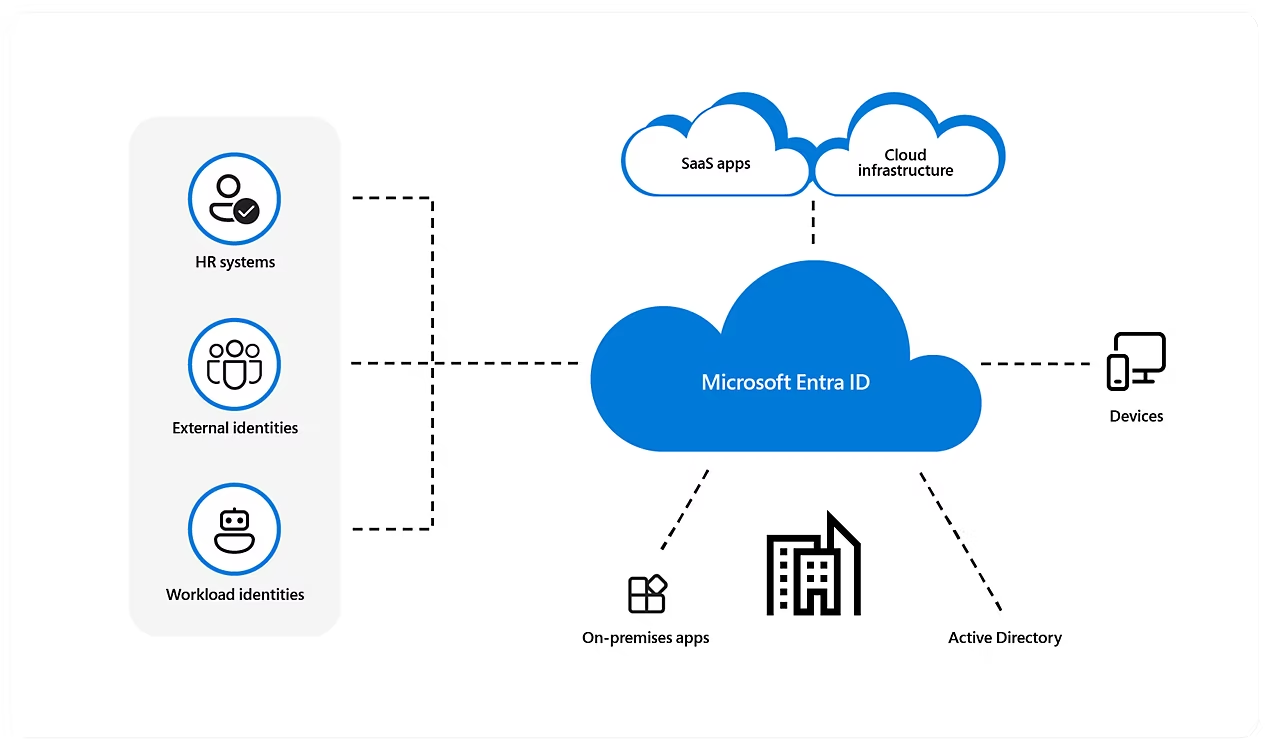
CloudServus is here to guide you from traditional on-premise directories to the modern world of device management with Microsoft Entra ID (formerly Azure Active Directory). Whether you’re exploring Co-Management, Microsoft Entra Join, or a Hybrid approach, we’ll help you unlock the benefits and navigate the complexities of Microsoft ID for a more connected environment.
Microsoft Intune streamlines software deployment, user access policies, encryption, and endpoint configurations across Windows, Mac, iOS, and Android devices. With Intune, you gain consistent software deployment and robust security measures, including encryption to protect sensitive data. Customize configurations and manage inventory for all devices in one place. Let Intune empower your organization’s device management and elevate security standards.
Want to simplify endpoint device provisioning? Windows Autopilot seamlessly integrates with Microsoft Intune, streamlining deployment straight from leading manufacturers like Dell and HP.
With Windows Autopilot, setup is effortless. When users log in for the first time, their devices are automatically connected to Microsoft Entra ID and enrolled with Intune/SCCM. This allows all company apps and policies to deploy directly to their devices. Say goodbye to manual setup and complex distribution—Autopilot handles it for you.
Windows Autopilot is your ultimate time-saver, letting you focus on what matters—boosting productivity and efficiency. Transform your endpoint management with Windows Autopilot and make device deployment a breeze.
When your organization transitioned to remote work, you quickly adapted to keep your team productive. But in the rush, your endpoint management may have taken a backseat.
If you missed the chance to secure devices or set up safeguards against data breaches, it’s not too late. Now’s the time to revisit and strengthen your endpoint management system to protect your data and support your remote team with confidence.
Let's Connect