Azure and Microsoft 365 Security: What are Security Defaults?
Microsoft recently released Security Defaults to help customers make their Microsoft 365 and Azure environments more secure FOR FREE. Before you...

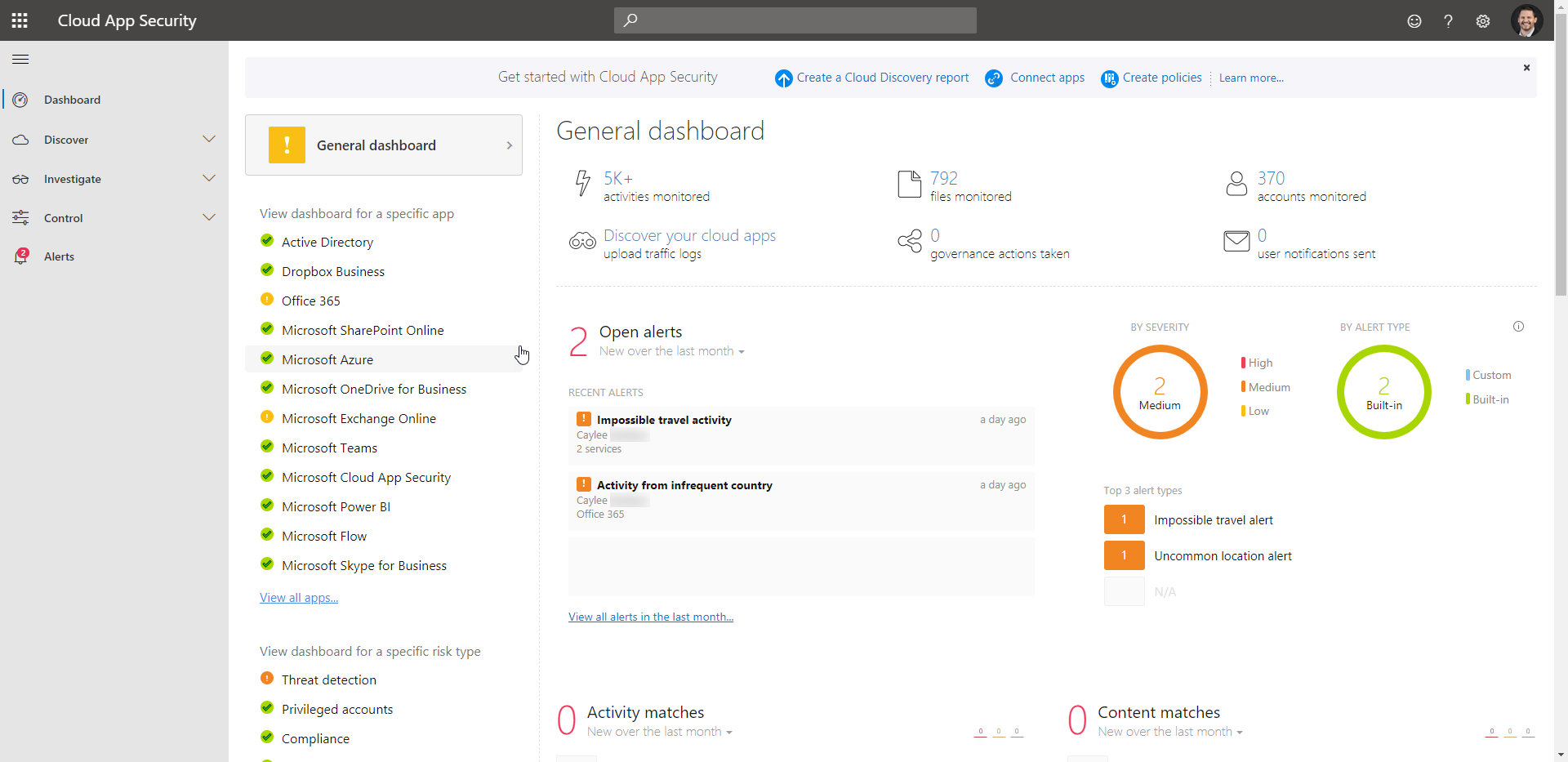
Microsoft Cloud App Security continues to impress our customers and us with its capabilities! I’ll abbreviate it as MCAS, because anyone who works in the Microsoft space will know that there are way too many “CAS” acronyms. Haha. If you haven’t heard of Cloud App Security it is Microsoft’s version of a Cloud Access Security Broker (CASB) released in 2018. It ranked highest in Execution on Gartner’s latest Magic Quadrant for CASB. Here is how Microsoft describes it:
Microsoft Cloud App Security is a multimode Cloud Access Security Broker (CASB). It provides rich visibility, control over data travel, and sophisticated analytics to identify and combat cyberthreats across all your cloud services.
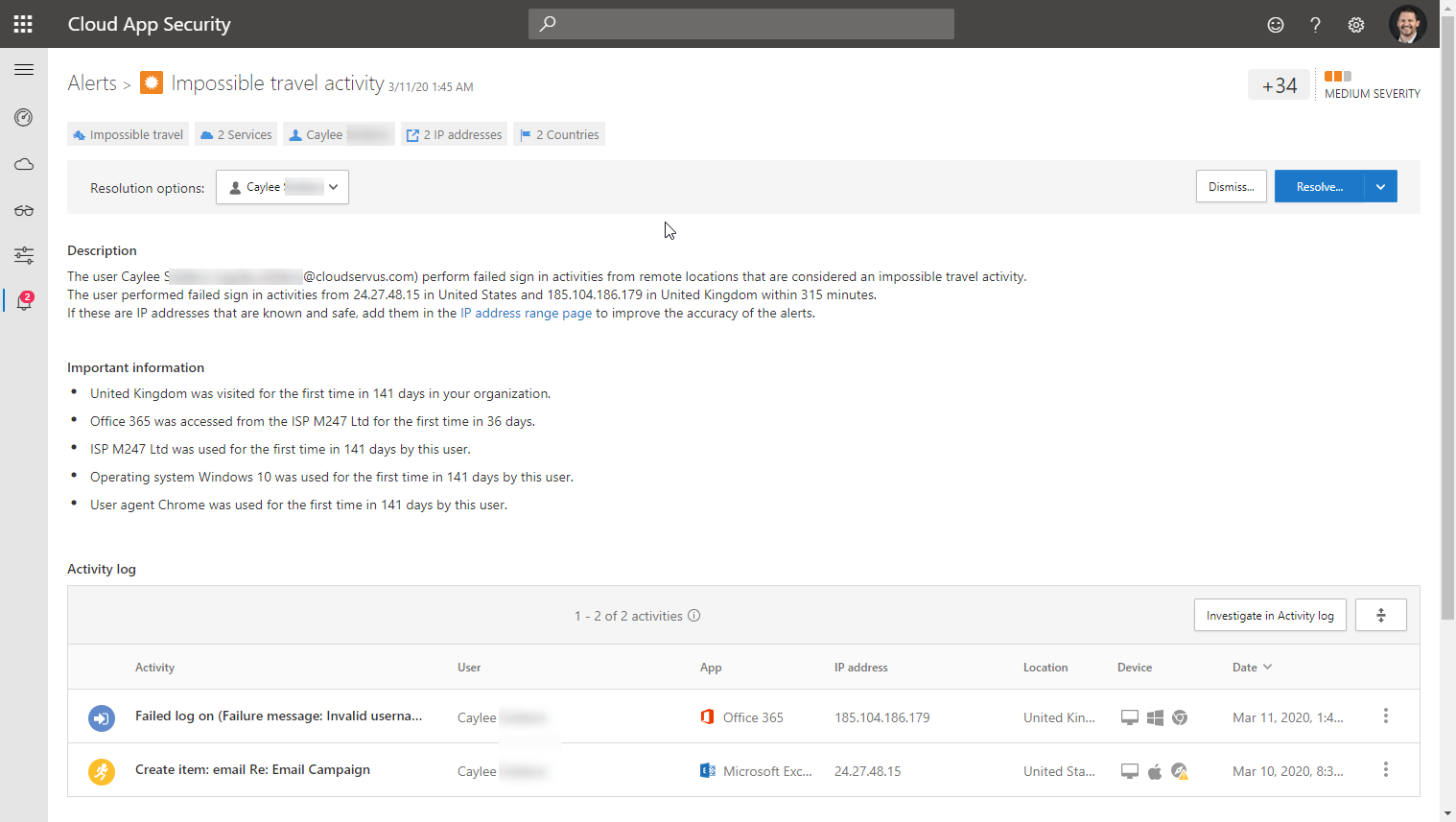
If you have not implemented it, then you should! We run it internally and last night was another great example of how Microsoft is using Machine-Learning and AI to protect our resources in the cloud. We also have text messaging alerts set up for some threats that appear in MCAS, so we received a text message at 1:45am last night for “Impossible travel activity” and “Activity from infrequent country“. It looks like someone was trying to login to one of our employee’s accounts from the UK. “Big deal” you might say, “a lot of tools alert you for logins from other countries”. This was much more in-depth analysis when you dig into the alerts.
Let’s take a look at the “Impossible travel activity” first. You’ll notice multiple things in the Description and Important information sections, but I want to highlight that MCAS actually looked at a successful login in the US and a failed login from the UK within 315 minutes of each other. Last I checked commercial super-sonic flights ended with the Concorde, so it’s pretty difficult or “Impossible…” by MCAS’ standards to get from Austin, Texas to the UK in a little over 5 hours. That’s pretty damn cool!
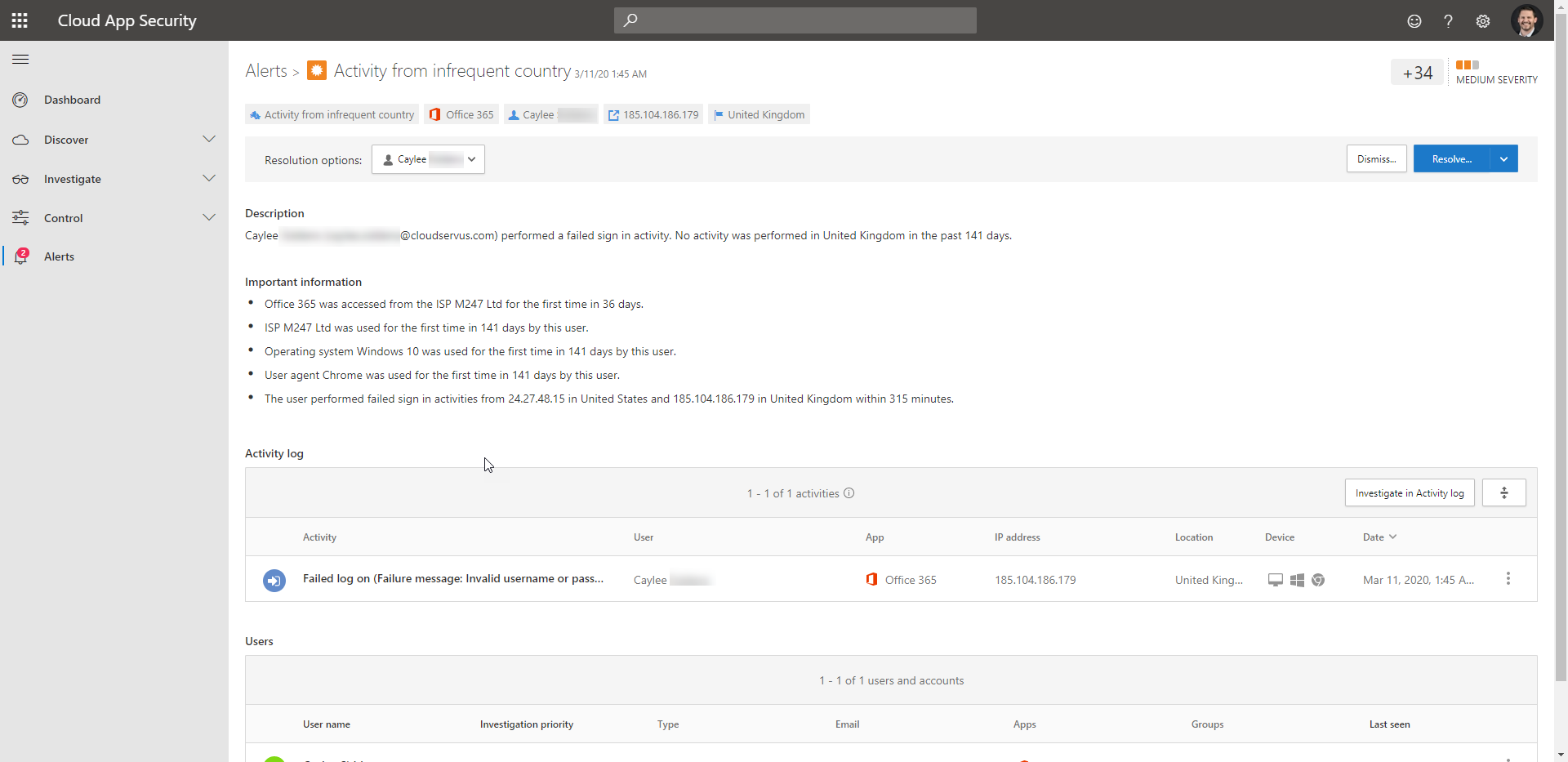
The Infrequent country alert was a little more mundane of a notification, but still very helpful when you’re trying to minimize risky user sign-ins to your Office 365 or Azure environment.
If you are interested in learning more and testing some of these capabilities in your environment, check out our Cloud Security Assessment where we leverage the tools you’re probably already licensed for, to check your security posture. We live in a Zero Trust world! It’s time to protect your environment from ever-present threats.

Microsoft recently released Security Defaults to help customers make their Microsoft 365 and Azure environments more secure FOR FREE. Before you...

CloudServus Achieves additional Microsoft Gold Partner Competency in Cloud Platform CloudServus is very proud to announce that they have attained ...

Pricing and Feature Changes Coming to Microsoft Endpoint Manager (Intune/SCCM) Microsoft is adding extra security and management functionality into...